Bluetooth gadgets consisting of cell phones, PCs, IoT gadgets are supposed to be vulnerable against the new BIAS Bluetooth attack or Bluetooth Impersonation Attacks.
Millions of Bluetooth gadgets including cell phones, PCs, IoT gadgets are supposed to be vulnerable against the new BIAS Bluetooth attack or Bluetooth Impersonation Attacks.
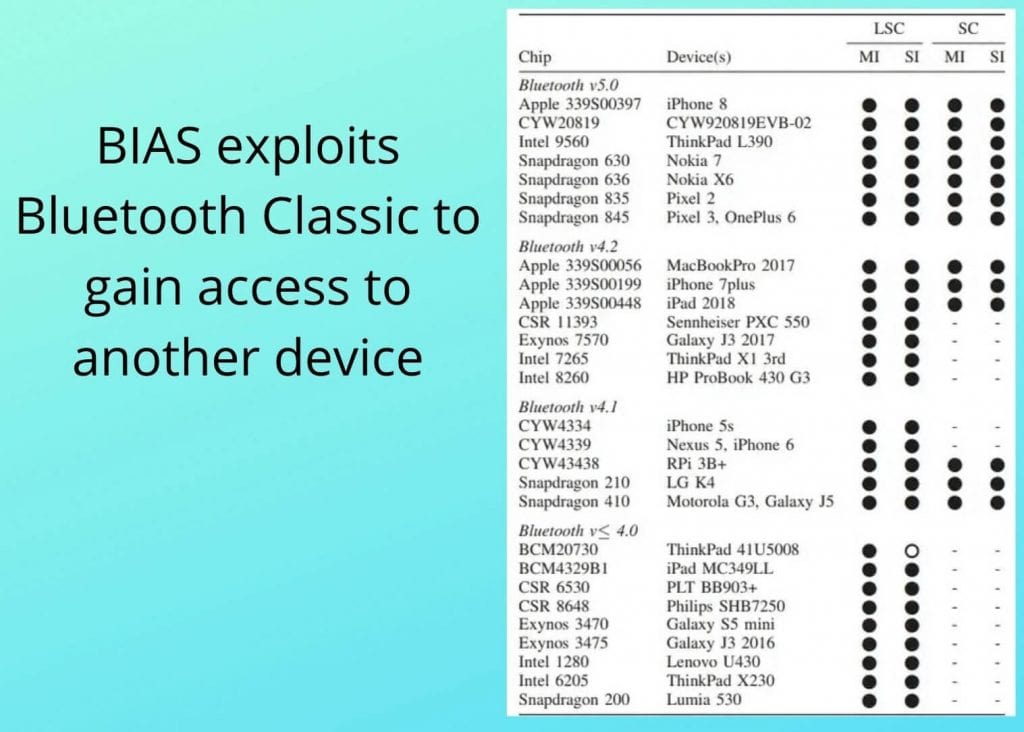
As indicated by specialists, the new BIAS attack can harm many Bluetooth gadgets and firmware from OEMs, for example, Apple, Cypress, Intel, Samsung, and others.
Specialists said in an announcement that “We utilize our techniques to check that the vulnerabilities in the verification mechanism are to be present in gadgets like smartPhones.
We effectively attack 31 Bluetooth gadgets (28 extraordinary Bluetooth chips) from significant hardware and software sellers, speaking to all the major Bluetooth renditions, including Apple, Qualcomm, Intel, Cypress, Broadcom, Samsung, and CSR,”.
Bluetooth is a prevalent innovation for remote correspondence utilized by billions of gadgets and the Bluetooth standard incorporates a legacy confirmation strategy and a protected verification system.
The BIAS security bug uses the way that gadgets handle connection keys or long term keys that are created when two Bluetooth gadgets paired with each other.
Some Important Points :-
Analysts noted that “Since attack influences all gadgets which having Bluetooth we played out a mindful divulgence with the Bluetooth Special Interest Group (Bluetooth SIG) – the organization that manages the improvement of Bluetooth norms – in December 2019 to guarantee that workarounds could be set up“.
In the meantime, the Bluetooth SIG said in a press note that the Bluetooth Core Specification has been refreshed to keep safe the devices and to minimizing the Bluetooth Classic Protocol from a “secure authentication method” to a “legacy authentication mode ” where the BIAS attack is profitable.
Bluetooth SIG said in an announcement that “To cure this vulnerability, the Bluetooth SIG is refreshing the Bluetooth Core Specification to explain when job switches are allowed, to require common verification in legacy confirmation, and to appoint checks for encryption-type to evade a downgrade of secure associations with legal encryption.
These progressions will be brought into a future detail amendment“
What is Bias Attack
The BIAS security defect exists in how gadgets handle the connection key, also called as long-term key.
This key is created when two Bluetooth gadgets paired with each other for the very first time.

BIAS BLUETOOTH ATTACK
They allow on a long-term key, which they use to conclude meeting keys for future associations without pushing gadget proprietors to experience the long process with each time the Bluetooth gadgets need to communicate.
Specialists said they found a bug in this post-bounding authentication process.
The defect can permit an invader to ridicule the personality of a formerly matched/fortified gadget and effectively validate and interface with another gadget without realizing the long-term key that was recently created between the two devices.
When a BIAS attack is active, the attacker would then be able to access or imply a responsibility for another Bluetooth Classic gadget.
The group of specialists said they tried the attack against a wide scope of gadgets, including cell phones (iPhone, Samsung, Google, Nokia, etc), tablets (iPad), PCs (MacBook, HP Lenovo), earphones and system-on-chip board (Raspberry Pi, Cypress).
Analysts said that “At the time of writing, we had the option to test Bluetooth chips from Cypress, Qualcomm, Apple, Intel, Samsung, and CSR.
All gadgets that we tried were vulnerable against the BIAS attack,”.
Merchants of Bluetooth gadgets are relied upon to turn out firmware updates in the coming months to fix the issue. The status and availability of these updates are as of now hazy, in any event, for the analysts’ group.
Conclusion
At Last, As per the Github Page of the BIAS attack, this type of vulnerability was pointing out to the Bluetooth SIG group – the organization that watches the development of Bluetooth protocol, in December 2019. However, at the time of the declaration, the team tested chips from Cypress, Qualcomm, Apple, Intel, Samsung, and CSR. It was found that all these devices were vulnerable to the BIAS attack. The team stated that some vendors might have implemented workarounds on their devices so if a user’s device was not updated after December 2019, it may be vulnerable.
Read More:
I like this web site very much so much fantastic information.
thanks for your love!